Before jumping into the way of hackers trying to accomplish their task of running malware exe files on MacOS, it is important to know about the statement and the terms first.
- Hackers are the people who use technology to gain unauthorized access to a data ethically or unethically.
- Malware is a ware or software designed to corrupt or interfere in the normal functioning of a computer system.
- EXE Files are the files in an executable format. EXE is the file format.
- MacOS is a series of operating system developed by Apple.
There are gazillions of programs and software released every day and to identify amongst them which one is malware and a threat can be a really daunting task. To get some relief from this task one should run proper patching routine. Here, patching routine refers to looking after the files that have a software update program inserted into it. Also, many devices and programs try on themselves to get automatically updated but then some of them are still left vulnerable to the threat.
Malware can be broadly categorized into three categories:
- Viruses: Virus is a code which can replicate on its own and cause damage to the system.
- Worms: Worms are also, but they can also travel around on their own in a network system with destructive intentions.
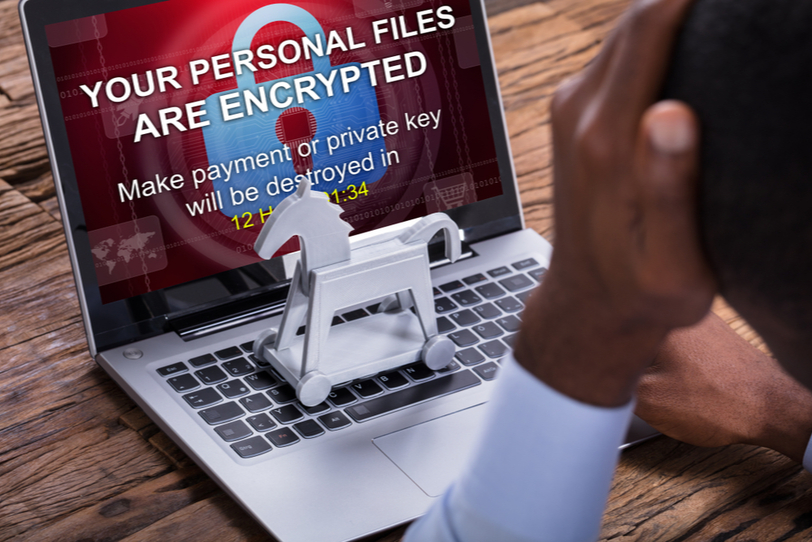
- Trojan horses: These are the programs that appear to be non-harmful but in fact work on corrupting the computer system.
These malware programs enter into your system through web pages or emails. Initially, a system gets corrupted through a stub downloader program. The stub program then leads to downloading of various other programs and malware that are designed so as to be undetected and cannot be removed. A person who creates this kind of malware can also be paid by a company to collect the confidential data of his rivals.
The most trusted way of hackers to get into someone else’s computer without his knowledge is to be hidden, and they have developed quite a few methods for the same.
- A system runs a debugging program on its own, or a user runs the program. When such a program is run, the malware developers can get to know of these activities, and so they stop running the malware or change its behavior in such situations.
- Rootkits: These are the combination of tools and techniques that let the malware programs hide deep into the system and be undetected.
- Codes and processes: These are somewhat similar to the Trojan horses. These are downloaded by the user for a particular task, but other than doing the task assigned, its primary function is to get unauthorized access to the data. Some examples of this type of files are explorer.exe, notepad.exe, svchost.exe, etc.
Running an EXE file on Microsoft is a normal thing but running the files with .exe extension is a surprising phenomenon. Besides this, it is also capable of launching the malware and bypass the mac security mechanism Gatekeeper. These files cannot be run on Linux and MacOS, but it has been able to evade the Gatekeeper protection because it keeps a check only on native MacOS files.
The malicious file is introduced with the help of an application download inside the DMG file that pretends to be a well-known firewall app Little Snitch. Executable files are designed to be run on the Windows, and this Gatekeeper skipped the code signature check, and it got installed in the system.
This has opened up new opportunities for hackers to try evading into the MacOS system. They would now look for new ways to accomplish the same. This malware was spotted in countries like United Kingdom, United States, Australia, South Africa, etc. Also, Little Snitch is not the only application with the executable file format but other applications such as Paragon, Wondershare are also responsible. The file was named as Installer.exe, and to the uttermost surprise, the file responded with error messages on Windows.
Once the installer.exe file finds a way into your MacOS, it seeks through information such as the name of the model, device Ids, processor specifications, RAM, etc. The malware also sends information about the applications installed to its server. Meanwhile, it also downloads several other applications and programs on the system.
If you encounter a .exe file at your MacOS, you can always convert it into forms suitable for your system through these applications:
-
Cameyo:
This application was launched in the year with an aim to run Windows enabled applications on other devices as well.
-
Ceedo:
A portable operating system that allows users to run applications in a virtual environment.
- Citrix
- VM Ware Fusion
- Parallels Desktop
- Microsoft Application Virtualization
Many of these apps are free while some cost money but all of these can help you with the task.
Tips to safeguard your computer from malware:
- Do not install pirated versions of applications. If you really need a program, and really, really aren’t prepared to pay for it, first try to find a free alternative.
- Always download programs from official sources: the App Store or developer websites.
- If due to any reason you had to download an application from a non trusted source always check what has been downloaded and be suspicious of any extra activities on your system.
- Use an antivirus system that is protected and reliable.
- Always keep your antivirus system up to date. Give a routine check-up.
- Run scheduled scans regularly provided by your antivirus system. Do not postpone things.
- Keep your operating system current.
- Secure your network while connecting with passwords and that too a strong password.
- Double check the files downloaded. Do not open an email attachment from a person or organization you are not perceived with.
- Keep your personal information safe and confidential.
- Do not use open Wi-Fi
These tips are sure to help you through the hackers in new innovative ways.
Contact us today to learn about Bleuwire™ services and solutions in how we can help your business.





